Beyond IAM: Temporary Cloud Access That Works Across AWS and Azure
|
AWS FOR THE REAL WORLD
⏱️
Reading time: 9 minutes
🎯
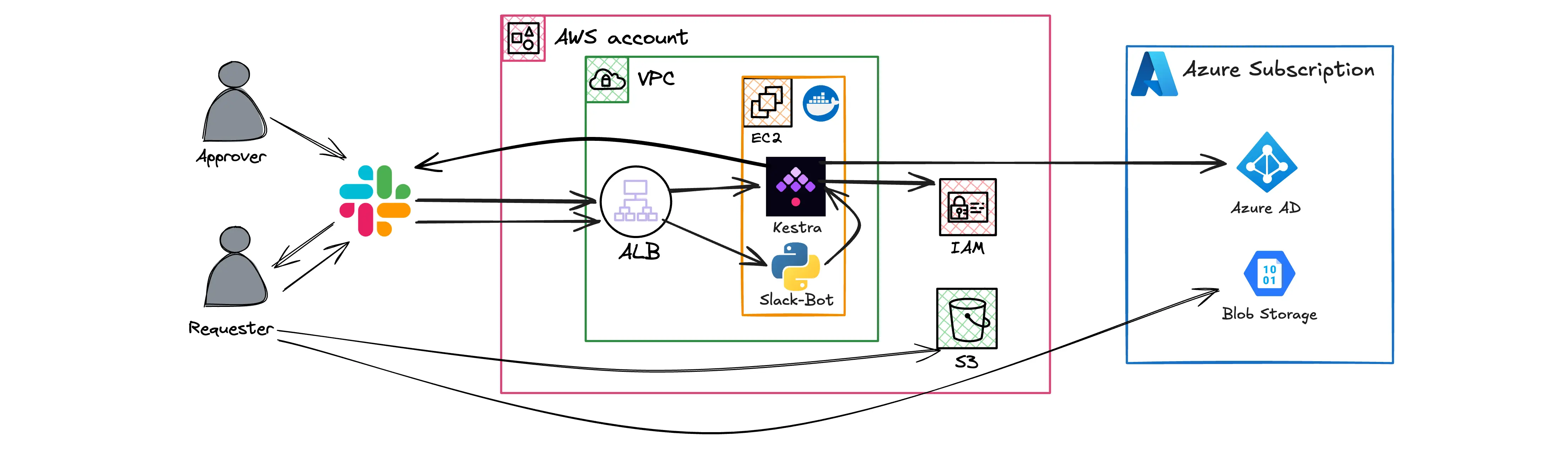
Main Learning: Build a self-service portal that grants temporary AWS + Azure access and revokes it automatically — using Kestra and one YAML file.
Hey Reader 👋🏽 Happy new week! Tobi and I met up last week and spent some time planning the videos ahead. We’re going more and more into YouTube — and a few things I’m hyped about:
We love AI. But we still want to teach the real-world basics that nobody else covers. Which is exactly why I’m excited about today’s sponsor: Kestra. I’ve talked a lot about TEAM — the AWS solution for automating temporary admin access. TEAM is great. But it has one hard limit: your devs almost always need access to more than just AWS. The moment Azure or another cloud enters the picture, TEAM stops at the door. This is where Kestra comes in. Rather watch a video? We’ve recorded one for you 👇🏽 This issue is sponsored by Kestra. We only partner with tools we'd actually use ourselves.
Amazing that you're reading until here! Check out Kestra here :) Have a great week ahead! |
AWS for the Real World
We teach AWS for the real world - not for certifications. Join more than 10,500 developers learning how to build real-world applications on AWS.
AWS FOR THE REAL WORLD ⏱️ Reading time: 12 minutes 🎯 Main Learning: Most of the complaints in the viral "leaving AWS" post are skill issues — but egress pricing is a fair hit. 📝 Blog Post Hey Reader 👋🏽Recently, a post with the title "I returned to AWS and was reminded why I left" hit 810 upvotes on Hacker News last week and went pretty viral with it.I read it twice before forming an opinion. My honest take: most of the complaints are skill issues! 🤷♂️Nevertheless, the post is well written and...
AWS FOR THE REAL WORLD ⏱️ Reading time: 10 minutes 🎯 Main Learning: Describe the agent: model, prompt, tools and AWS runs the orchestration loop behind one API call! 📝 Blog Post Hey Reader 👋🏽 If you've ever built an agent on AWS, you know the pain: glue Bedrock, Lambda, and DynamoDB together, grab LangGraph or Strands, then also own the orchestration loop, the memory layer, and your own tracing. 😅 A "simple" agent ends up with multiple layers of pain.AWS just shipped something that takes most...
AWS FOR THE REAL WORLD ⏱️ Reading time: 12 minutes 🎯 Main Learning: Wrapping a multi-account AWS org in multiple layers of guardrails, featuring SCPs, RCPs, CloudTrail and Bugdet Actions 📝 Blog Post Hey Reader 👋🏽As you hopefully know, we're really obsessed with security, observability and auditability. That's why we've carefully crafted our AWS Organization's setup. 🏗️ In this issue, we want to walk you through our most important guardrails! Including all the whats and whys. 😊 Sponsored AWS...