AWS just shipped an AI on-call engineer. We tested it.
|
AWS FOR THE REAL WORLD
⏱️
Reading time: 12 minutes
🎯
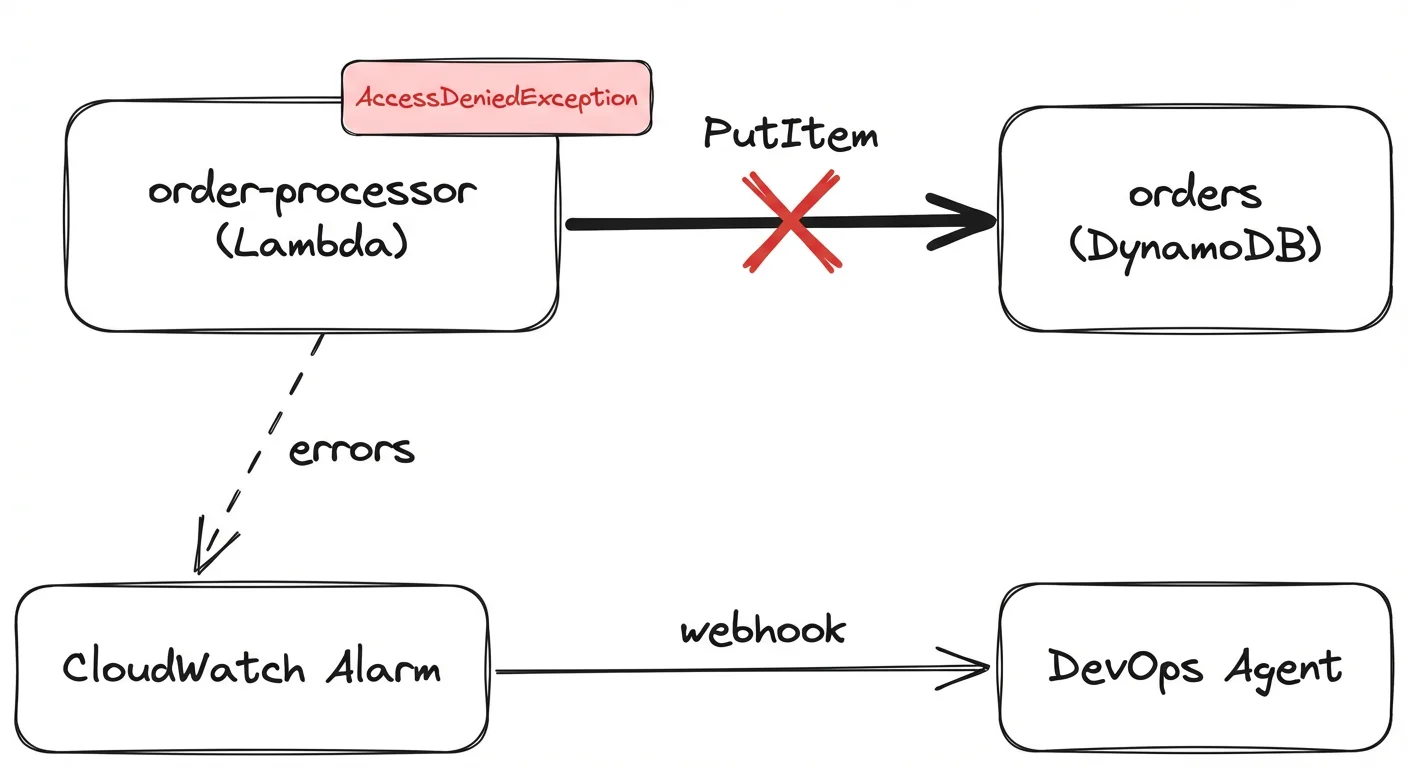
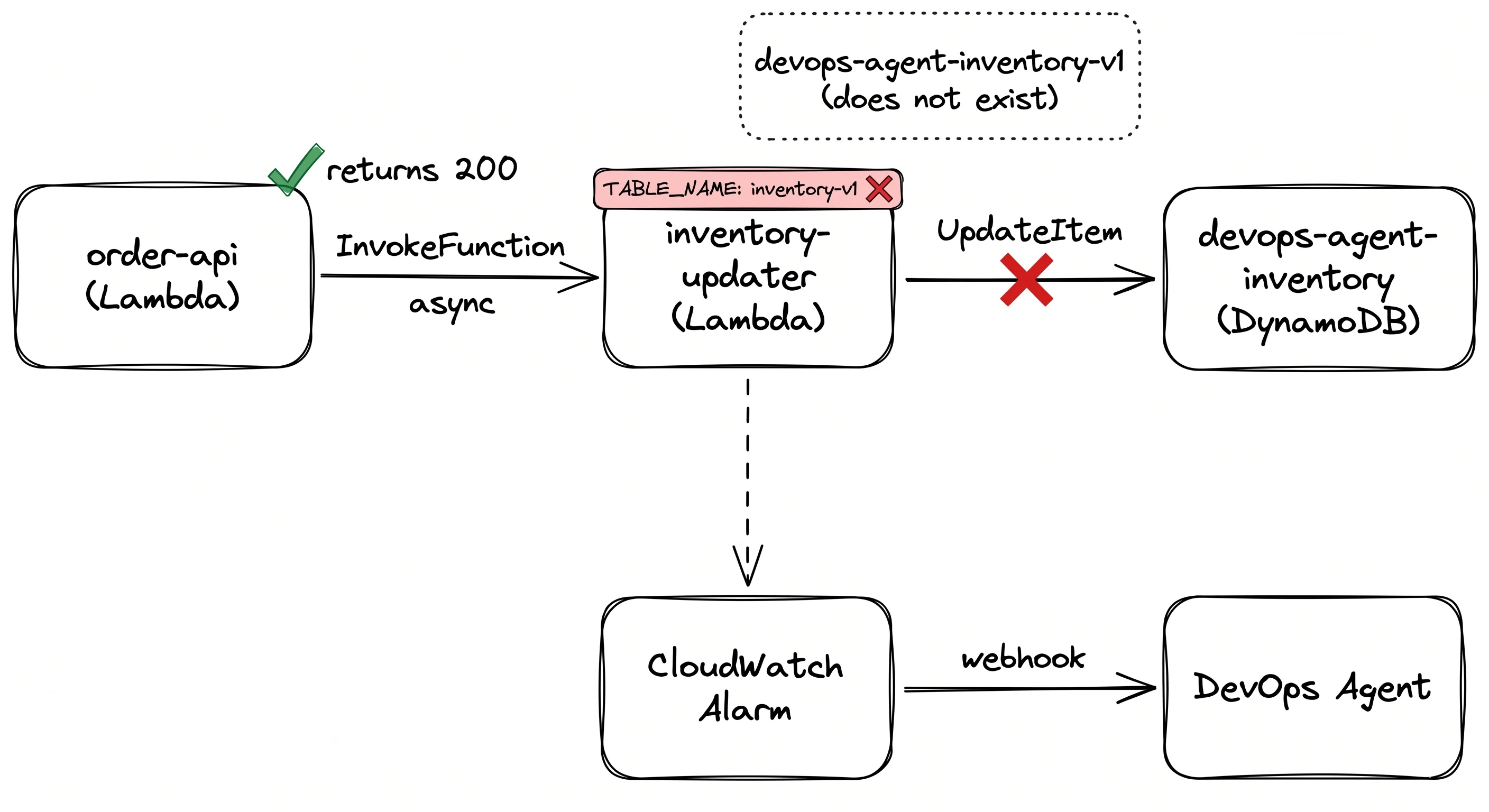
Main Learning: AWS DevOps Agent investigates incidents autonomously across CloudWatch, CloudTrail, and your
code. It surfaces evidence brilliantly — but can confidently point at the wrong root cause, so don't apply its fixes blindly.
Hey Reader 👋🏽 I was in Portugal for the past week. 10 days of tennis, padel, sun and waves 🎾 Highly recommended place!
… and honestly I love it. Every company is adding AI features now. Not all of them make sense. Also AWS is known for new AI features. One of the last ones: AWS DevOps Agent. Tobi checks it out in real-live, let's see what it can do! This issue is sponsored by Coder.
That's a wrap. Sandro & Tobi |
AWS for the Real World
We teach AWS for the real world - not for certifications. Join more than 10,500 developers learning how to build real-world applications on AWS.
AWS FOR THE REAL WORLD ⏱️ Reading time: 12 minutes 🎯 Main Learning: Wrapping a multi-account AWS org in multiple layers of guardrails, featuring SCPs, RCPs, CloudTrail and Bugdet Actions 📝 Blog Post Hey Reader 👋🏽As you hopefully know, we're really obsessed with security, observability and auditability. That's why we've carefully crafted our AWS Organization's setup. 🏗️ In this issue, we want to walk you through our most important guardrails! Including all the whats and whys. 😊 Sponsored AWS...
AWS FOR THE REAL WORLD ⏱️ Reading time: 6 minutes 🎯 Main Learning: Three levels of AWS observability — from raw console.log to a Claude Code agent that queries CloudWatch for you. 📝 Blog Post 📂 Claude Code agent (free gist) 🎬 Watch on YouTube Hey Reader 👋🏽Quick check — when did you last close the CloudWatch console and feel like that was time well spent?Yeah, me too. And I'm done with it. In this week's video, I will show you how to never open the CloudWatch console again. As a good...
AWS FOR THE REAL WORLD ⏱️ Reading time: 10 minutes 🎯 Main Learning: S3 Files gives POSIX access at S3 prices: 13x cheaper than EFS for large files, but the 60-second write-back delay silently breaks coordination patterns! 📝 Blog Post 💻 GitHub Repository 🎬 Watch on YouTube Hey Reader 👋🏽 Sandro is currently traveling through Portugal - work and fun combined! If you happen to be around, reach out. Would be great to meet up! 🤝 This week we're digging into S3 Files: a POSIX file system backed by...