The Only Way to Grant Admin Access on AWS
|
AWS FOR THE REAL WORLD
⏱️
Reading time: 5 minutes
🎯
Main Learning: Deploy AWS's open-source TEAM solution for temporary admin access with approval workflows
Hey Reader 👋🏽 I hope you had a great weekend and have a great week ahead. One thing I see over and over again in AWS setups: admin permissions are either handed out way too easily or way too hard. There is no middle ground. In other systems this was already solved. You shouldn’t have to DM somebody for admin access. We don’t want to face it, but there are actions which only admins can do:
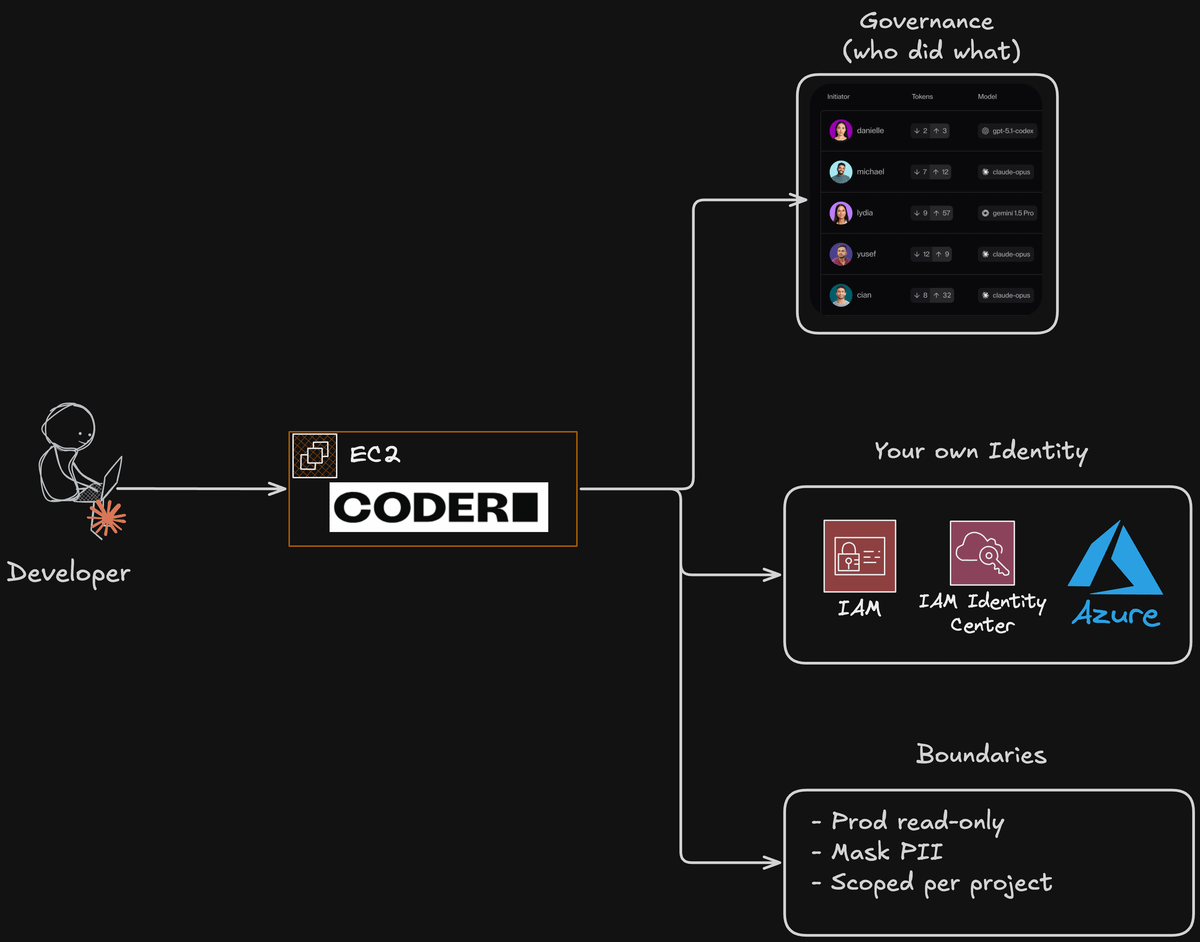
But first of all, let's look at our sponsor for this newsletter, which is Coder - start using AI Agents securely in your corporation. This issue is sponsored by Coder. Thanks for supporting AWS Fundamentals! Back to TEAM: Even if you don’t need admin access a lot, it still makes sense to have a process for it. What typically happens: you give your developers admin access and forget to take it away. This is where the TEAM application comes in. TEAM stands for Temporary Elevated Access Management. It’s an AWS sample (not a managed service) that handles the process of granting and revoking admin access automatically. In this issue, I show you how to set it up and how it works. Rather watch a video? I’ve recorded one for you!
That's it for this week! Sandro & Tobi |
AWS for the Real World
We teach AWS for the real world - not for certifications. Join more than 10,500 developers learning how to build real-world applications on AWS.
AWS FOR THE REAL WORLD ⏱️ Reading time: 10 minutes 🎯 Main Learning: Describe the agent: model, prompt, tools and AWS runs the orchestration loop behind one API call! 📝 Blog Post Hey Reader 👋🏽 If you've ever built an agent on AWS, you know the pain: glue Bedrock, Lambda, and DynamoDB together, grab LangGraph or Strands, then also own the orchestration loop, the memory layer, and your own tracing. 😅 A "simple" agent ends up with multiple layers of pain.AWS just shipped something that takes most...
AWS FOR THE REAL WORLD ⏱️ Reading time: 12 minutes 🎯 Main Learning: Wrapping a multi-account AWS org in multiple layers of guardrails, featuring SCPs, RCPs, CloudTrail and Bugdet Actions 📝 Blog Post Hey Reader 👋🏽As you hopefully know, we're really obsessed with security, observability and auditability. That's why we've carefully crafted our AWS Organization's setup. 🏗️ In this issue, we want to walk you through our most important guardrails! Including all the whats and whys. 😊 Sponsored AWS...
AWS FOR THE REAL WORLD ⏱️ Reading time: 6 minutes 🎯 Main Learning: Three levels of AWS observability — from raw console.log to a Claude Code agent that queries CloudWatch for you. 📝 Blog Post 📂 Claude Code agent (free gist) 🎬 Watch on YouTube Hey Reader 👋🏽Quick check — when did you last close the CloudWatch console and feel like that was time well spent?Yeah, me too. And I'm done with it. In this week's video, I will show you how to never open the CloudWatch console again. As a good...